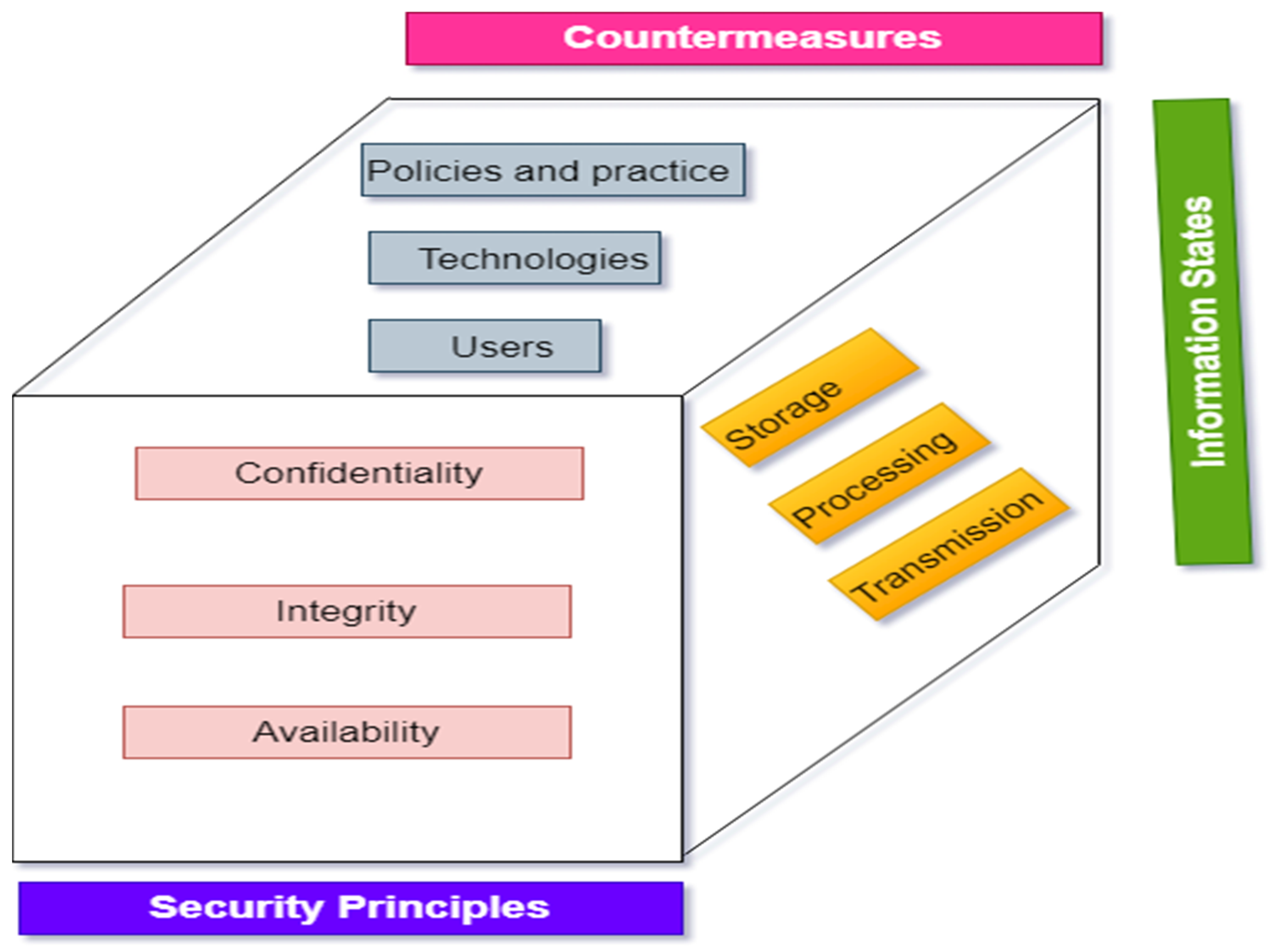
Electronics | Free Full-Text | A Comprehensive Review of Cyber Security Vulnerabilities, Threats, Attacks, and Solutions

Cyber Operations: Building, Defending, and Attacking Modern Computer Networks: O'Leary, Mike: 9781484242933: Amazon.com: Books

Cyber Operations: Building, Defending, and Attacking Modern Computer Networks: O'Leary, Mike: 9781484242933: Amazon.com: Books

Offensive Shifts, Offensive Policies: Cybersecurity Trends in the Government-Private Sector Relationship - Canadian Global Affairs Institute

Cyber Operations: Building, Defending, and Attacking Modern Computer Networks: O'Leary, Mike: 9781484242933: Amazon.com: Books

Forget a Whole-of-Government Cybersecurity Strategy—It's Time for a Whole-of-Nation Approach - Modern War Institute

Cyber Operations: Building, Defending, and Attacking Modern Computer Networks: O'Leary, Mike: 9781484204580: Amazon.com: Books

Cyber Operations: Building, Defending, and Attacking Modern Computer Networks: O'Leary, Mike: 9781484242933: Amazon.com: Books
Read PDF Cyber Operations: Building, Defending, and Attacking Modern Computer Networks: 2015 > QBOGDXWQ8HOW

PDF) Cyber Operations Building Defending And Attacking Modern Computer Networks by Mike O Leary | Annie R. Sonntag - Academia.edu
Future Internet | Free Full-Text | Adversarial Machine Learning Attacks against Intrusion Detection Systems: A Survey on Strategies and Defense

The Legend of Sophistication in Cyber Operations | Belfer Center for Science and International Affairs